Typora 1.9.5 Cracking
Locate and unpack the original
app.asarThere are three ways to unpack:
Directly drag
app.asarinto VSCode to open it — this method doesn’t require a Node.js environment but cannot repackUse the 7-zip asar plugin. Download the plugin from here, place it in the
Formatsdirectory under the 7-zip installation path, then openapp.asarwith 7-zip. This method doesn’t require Node.js and allows modifying files within the asar archive — recommended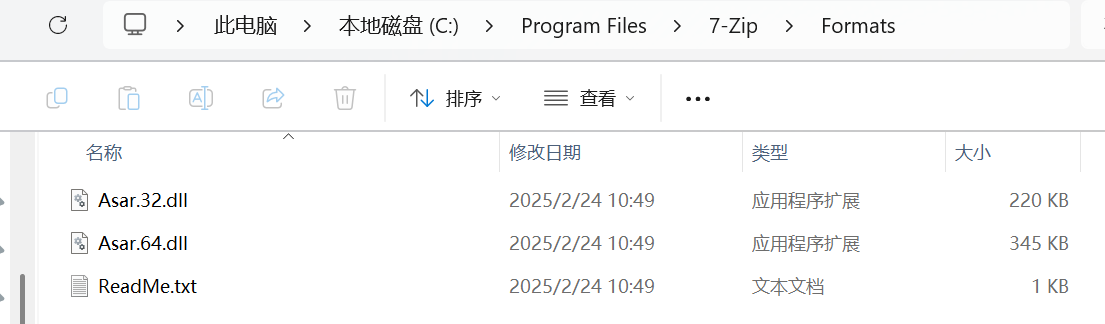
Install a
Node.jsenvironment and use the asar toolapt install nodejs npm install -g asar asar e ./app.asar ./app.asar.unpackedIf unpacking reports an error about
main.nodenot being accessible, copy one from the Typora directory to the path mentioned in the error.
The extraction yields 2 files:
atom.jsandpackage.json.atom.jscontains AES-encrypted base64 ciphertext that needs to be decrypted.Decrypt
atom.jsAES encryption requires a KEY and IV. The
atom.jsencryption scheme is:- KEY is provided by
main.node - IV is computed from the final
atom.jslength and the last byte of the file - The last byte does not participate in encryption
- AES-256-CBC encrypted, then base64 encoded
AES is symmetric — if you know the KEY and IV, simply reverse the process. The KEY is in
main.node. In version 1.9.5, the extracted KEY is0d8e841eb83ac8106208f45770bc39b9d8b8ab60b2fb4613284fb497b68b0c6a. The originalatom.jsafter base64 decoding has a total length of140593, with the last byte being0x6a. The IV is computed as47a91ac73cfaa5af60e1e1d54301e848. With all parameters ready, use CyberChef to decryptatom.js.- KEY is provided by
Modify
atom.js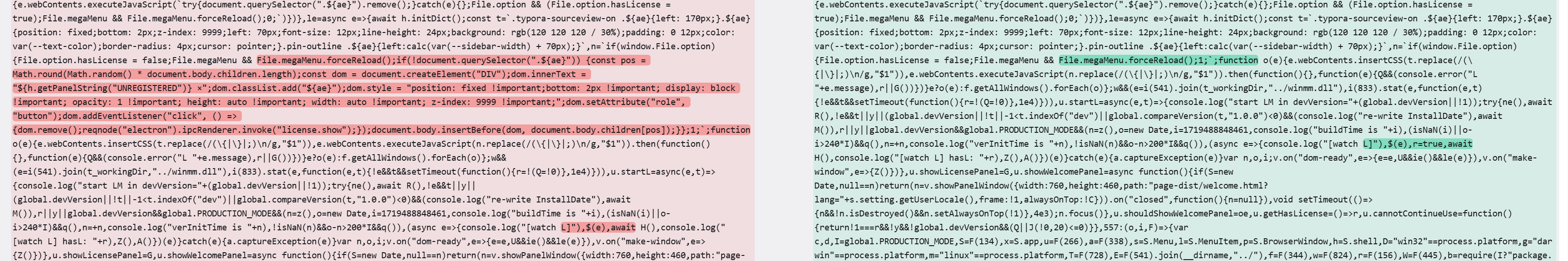
Re-encrypt
atom.jsAfter modification, first encrypt with an arbitrary IV to get the encrypted length
139968. If the ciphertext is appended with0xb7, the new length becomes139969. Use these two values to recalculate the IV, yieldingb820f7c793af30da91e80c12c6b83395. Re-encryptatom.jswith the KEY and new IV, then append\xb7. Encryption can be done usingopensslor CyberChef:openssl enc -aes-256-cbc -in ./atom.de.js -out atom.js -iv b820f7c793af30da91e80c12c6b83395 -K 0d8e841eb83ac8106208f45770bc39b9d8b8ab60b2fb4613284fb497b68b0c6a printf '\xb7' >> atom.jsRepack
app.asarPlace
atom.js,main.node, andpackage.jsoninto a directory (e.g.,new), then use the asar tool to pack:asar pack ./new app.asar --unpack "main.node"Replace the original
app.asarand restart
Locating the app.asar decryption code in main.node:
Search for the string
app.asar. The location nearindexOfis the target. After some NAPI function calls, execution jumps to another function that performs the decryption — the% 256operation within that function is essentially computing the IV.Key locations in version 1.9.5:
sub_180010BF0:app.asarcompilationsub_180004647:sub_18000B480wrappersub_18000B480:atom.jsdecryptionsub_180001992: IV generation — 3 parameters: array to receive the IV, pseudo-random seed computed from the last byte and length, and generation lengthsub_1800044DF: AES decryption
IV computation:
IV is generated by directly calling
sub_180001992inmain.node. (code snippet)
Reference: Typora Latest Version Reverse Analysis